Solr is an “open source search platform built upon a Java library called Lucene. Solr is a popular search platform for websites because it can index and search multiple sites and return recommendations for related content based on the search query’s taxonomy.” Solr product features include “full-text search, hit highlighting, faceted search, real-time indexing, dynamic clustering, database integration, NoSQL features, and rich documents (e.g. MS Word, PDF) handling.”
We bring a consultative approach to training that is based on our real-world Solr implementation. Through a mix of lectures, hands-outs, lab exercises, students will figure out how to apply best practices to create versatile, scalable and high performance Solr applications. All you require is your PC and heaps of questions.
Topics Covered:
Introduction to search, Apache, Open Source & Lucene/Solr
Terminology, Solr features & capabilities
Solr architecture overview
Planning the search application
Case-study: Patent Search
Analysis
More Solr features
Advanced querying
Lucene basics
Relevancy
GEO search
Best practices
Extending Solr
Machine Learning
Training IR(Information Retrieval)
Siddhast® is known worldwide for Information Retrieval consulting services and we are now helping others to become more proficient in Information Retrieval via 1 and 2-day training workshops.In all workshops attendees go through several sequences of short lectures followed by interactive, group, hands-on exercises. All training are delivered by one of our experts — engineers
IP-Initial®
Training programe is designed specifically for beginners, so as to provide them the knowledge about the importance of Intellectual Property Rights and its benefits
- IP awareness workshop
- IP awareness onsite workshop
- IP awareness remote training
Scientific Information Retrieval
There are various patent databases and scientific information tools, which need certain skill sets to retrieve the information in a cost effective way. Keeping this in mind, we have designed a workshop on Scientific Information Retrieval, which is projected to enhance the online searching skills of individual through the powerful features of Patent Search tools. This designing has been done after untiring efforts so as to provide the clients with an insight to index patent databases. The workshop is aimed at brushing up the skills, which are needed to conduct comprehensive, yet cost-effective, searches. Also, it will make search easier and precise, thereby, giving a clear view about the patents and the scientific information.
- Scientific Information Retrieval awareness workshop
- Scientific Information Retrieval awareness onsite workshop
- Scientific Information Retrieval awareness remote training
IT-Training
Even with well-defined processes and a properly implemented enabling architecture, you still need people to make it all happen. Those people need to be equipped with the knowledge of how to use the architecture to execute the process; they need to understand why what they do is important and the value it brings.
We know the industry and its tools inside and out, and we can give you the knowledge you need not only to make it all work, but to show your user community the value it brings to your enterprise. Moreover, we help you understand how to adapt your messaging to different constituencies and contexts so you’re transferring the right knowledge to the right people.
Professional Training Service
specialized training or advanced professional learning intended to improve the professional skills, knowledge, competence, and effectiveness.
Scope of this service includes as:
– Providing training to the client employees as per the prescribed requirement.
– Providing the content and material required to all the trainees during the training session.
– Provision of appropriate induction kit (if required) or mention by client with appropriate content including complete schedule of the training, stationary (if required), study material etc.
Siddhast Obligations
· Training content and material in accordance with the rank/job of the trainee.
· All the training planning and control provided
·Training content clearly defined around the client requirement.
· Exam/review after the completion of course/subject to check the trainee’s understanding on topic.
· expertise and equipped on the subject matter of the training to be conducted.
· Training curriculum/content, methodology and training plan (both theory and practical) as per syllabus recognized by certifying agency.
· In case client has requirement of conducting examination for the trainees, Siddhast ensure assessment and declaration of results within 30 days of completion of batch. If a candidate fails in the assessment, then she/he is retrained for re-assessment and certification.
- Artificial Intelligence
 ARTIFICIAL INTELLIGENCE FOR EVERYONE Artificial Intelligence is not only for engineers. Artificial Intelligence provides customized machine learning programming and consulting to help your business discover the power of artificial intelligence. With our AI as a service offering, we deliver cutting-edge technology that allows you to make better, data-driven decisions. We teach machines to make predictions and recommendations, ...Know more
ARTIFICIAL INTELLIGENCE FOR EVERYONE Artificial Intelligence is not only for engineers. Artificial Intelligence provides customized machine learning programming and consulting to help your business discover the power of artificial intelligence. With our AI as a service offering, we deliver cutting-edge technology that allows you to make better, data-driven decisions. We teach machines to make predictions and recommendations, ...Know more - IT Support Professional CertificateIT Support Professional Certificate A job in IT can mean in-person or remote help desk work, either in a small business or at a global company. By earning an IT Support Professional Certificate, you can go from beginner to job ready in as little as eight months. Through a mix of video lectures, quizzes, and hand-on ...Know more
- SolrSolr is an “open source search platform built upon a Java library called Lucene. Solr is a popular search platform for websites because it can index and search multiple sites and return recommendations for related content based on the search query’s taxonomy.” Solr product features include “full-text search, hit highlighting, faceted search, real-time indexing, dynamic ...Know more
- Machine LearningMachine LearningKnow more
- Training IR(Information Retrieval)Siddhast® is known worldwide for Information Retrieval consulting services and we are now helping others to become more proficient in Information Retrieval via 1 and 2-day training workshops.In all workshops attendees go through several sequences of short lectures followed by interactive, group, hands-on exercises. All training are delivered by one of our experts — engineers Training ...Know more
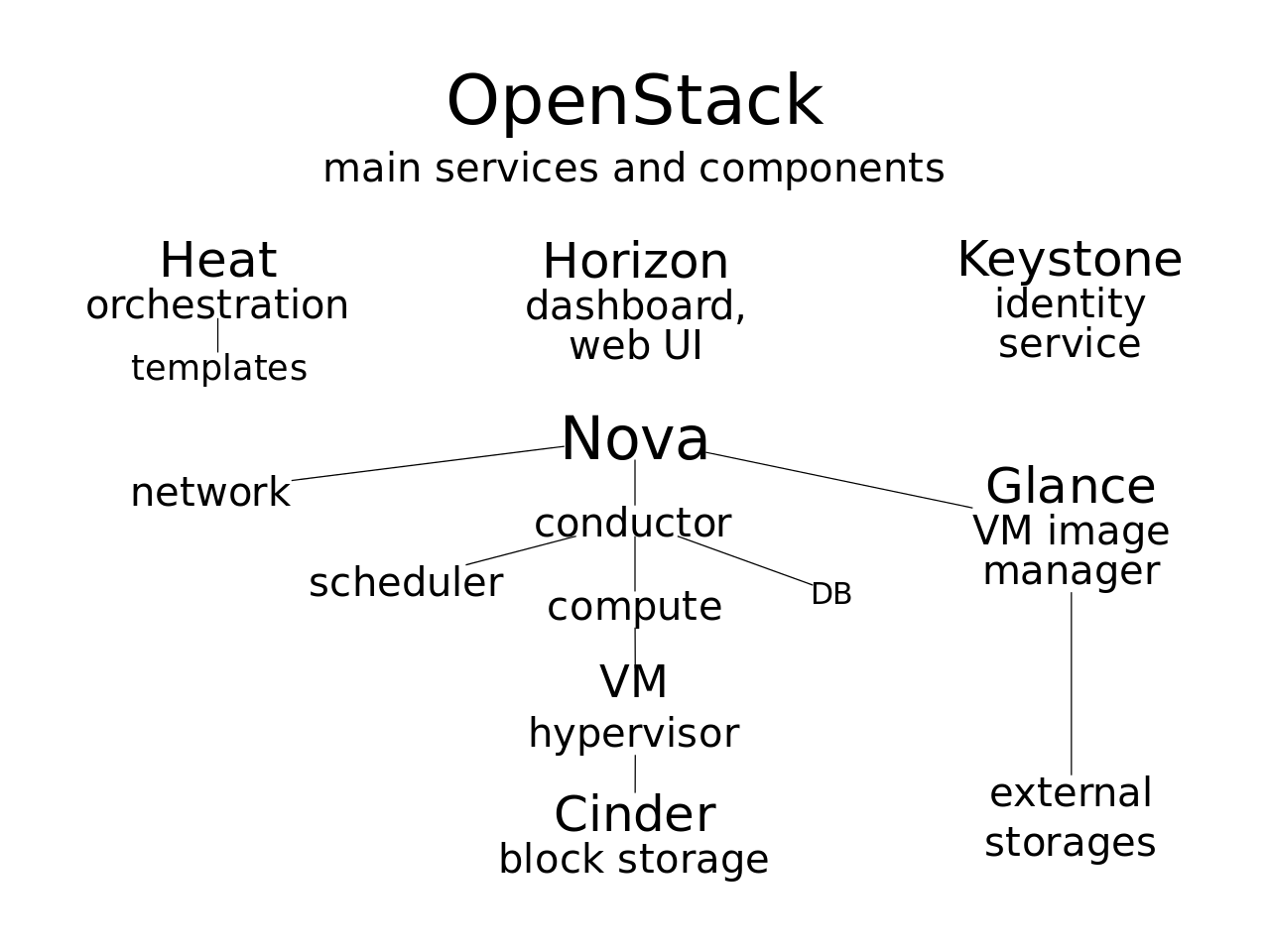
Open Stack
Clouds Infrastructure
Cloud infrastructure refers to the hardware and software components — such as servers, storage, a network and virtualization software — that are needed to support the computing requirements of a cloud computing model.
- Virtual Machine (Compute)Virtual Machines (VM) provide the basic IT Infrastructure that can be used by the Government Organizations to run their variety of workloads such as compute-intensive workload, memory-intensive workload, general-purpose workload, etc. All Virtual Machine packages, listed below, are Managed Virtual Machines. CSPs are required to list their prices on GeM platform keeping this in mind. ...Know more
- Storage ServicesThe Storage services can be defined in various categories Object Storage, File Storage, Block Storage, and Archival Storage. The Managed Storage Services is a storage infrastructure that is provisioned keeping the user needs in mind. Service Scope The Storage services can be defined in various categories Object Storage, File Storage, Block Storage, and Archival Storage. The Managed ...Know more
- Office productivity suiteThis service provides Office coverage for desktop, laptop, tablets and smart phones (Android, iOS and Windows) with per user subscription install rights. There is no need to pay for version upgrades; updates are included in the subscription along with new features roll out regularly.Know more
- Identity and Access Management – Security ServicesThis service may be used to authenticate and authorize users and computing resources within a network by assigning and enforcing security policiesKnow more
- Firewall (Virtual/ Physical)This service is used to monitor and control the incoming and outgoing traffic of a subnet by configuring some rules.Know more
- Managed Database as a Service (Advance)Database as a Service is a managed service offering by the Cloud Service Providers wherein in operating system and all low level components such as drivers, I/O, network, etc. are managed and optimized by the Cloud Service Providers. All objects created using “Database as a Service” are transparent to the underlying operating system. Activities such as OS management, antivirus, ...Know more
- Log AnalysisThis service may be used to generate insights from of the logs, by running queries against these logs. The service must retain the log for at least 30 days.Know more
- Hardware Security ModuleThis service can be used where a dedicated hardware security module is required to create, manage and control keys. The HSM must comply with FIPS 140-2 Level 3 requirements.Know more
- Database LicencesSiddhast offer database licenses to Government Organizations which they can use in that particular CSP’s Cloud environment. These are unmanaged databases. All these databases would have enterprise support included.Know more
- Container computer serviceContainers are the lightweight alternatives to Virtual Machines. Containers allow to encapsulate an application’s code, libraries, configuration and other dependent files into one single package. This packaging of the application and its dependent files offers improved developer productivity and environmental neutrality. The developers can continue focusing on improving/updating their applications without being worried about the ...Know more
Digital Signatures
Digital Signatures –Retail Price List
| Class of DSC | Validity | Purpose | Rate | Application form |
| Class 2 Individual | 2 yrs | ROC , Income Tax, BMC tenders | Rs.1150 |  |
| Class 3 Organisation | 2 yrs | e-Tenders/trademark, patents | Rs. 4000/- |  |
For USB token add Rs.600/- extra
| Documents | Individual Class 2 | Individual/Organisation Class 3 |
| Address Proof Individual | Any one
|
Any one
|
| Id Proof individual | Any One
|
Any One
|
| Id proof Organization | Any One(attested copy by partner or CS)
Attested Copy Of the Organisation PAN Card |
|
| Address proof Organization | Any One
|
|
| Authorization letter In favor of the certificate applicant from the Organization as per format below |
Ensure that the form is signed and the Name , email address and PAN numbers are correctly filled on the form Attach the required ID and Address proof documents as detailed above. The documents should be self / CA attested.Send the completed form along with payment to the following address:
Siddhast Intellectual Property Innovation (P) ltd, Delhi: +91 9871549769, +91 7376314900
Cyber Security
Cybersecurity is the protection of internet-connected systems, including hardware, software and data, from cyberattacks.In a computing context, security comprises cyber security and physical security — both are used by enterprises to protect against unauthorized access to data centers and other computerized systems. Information security, which is designed to maintain the confidentiality, integrity and availability of data, is a subset of cybersecurity.
HAM (Hardware Asset Management)
Hardware Asset Management (HAM)
Hardware Asset Management (HAM) is the management of physical components (desktops, laptops) and computer networks from the procurement stage to the retirement of the asset. HAM needs to be part of organisations overall scope and processes need to be aligned with other IT processes to ensure HAM is a big part of IT.
Just like software, hardware needs to be managed correctly to ensure the organisation is making the most out of the asset. Processes need to be in place to manage the asset from the point of request, to the moment the asset is retired.
Effectively managing hardware assets can also have an impact on the amount of time it takes to fix hardware problems. With the correct HAM processes in place, and a good education and understanding of said processes and hardware asset management in general, end users will see the time it takes to fix, request or procure hardware dramatically reduced. This in turn leaves the ITSM team to concentrate on other areas.
SAM (Software Asset Management)
Software asset management (SAM) is a business practice that involves managing and optimizing the purchase, deployment, maintenance, utilization, and disposal of software applications within an organization. According to the Information Technology Infrastructure Library (ITIL), SAM is defined as “…all of the infrastructure and processes necessary for the effective management, control and protection of the software assets…throughout all stages of their lifecycle.” Fundamentally intended to be part of an organization’s information technology business strategy, the goals of SAM are to reduce information technology (IT) costs and limit business and legal risk related to the ownership and use of software, while maximizing IT responsiveness and end-user productivity.SAM is particularly important for large corporations in regard to redistribution of licenses and managing legal risks associated with software ownership and expiration. SAM technologies track license expiration, thus allowing the company to function ethically and within software compliance regulations. This can be important for both eliminating legal costs associated with license agreement violations and as part of a company’s reputation management strategy. Both are important forms of risk management and are critical for large corporations’ long-term business strategies.
SAM is one facet of a broader business discipline known as IT asset management, which includes overseeing both software and hardware that comprise an organization’s computers and network.
Role within organizations
SAM can serve many different functions within organizations, depending on their software portfolios, IT infrastructures, resource availability, and business goals.
For many organizations, the goal of implementing a SAM program is very tactical in nature, focused specifically on balancing the number of software licenses purchased with the number of actual licenses consumed or used. In addition to balancing the number of licenses purchased with the amount of consumption, an effective SAM program must also ensure that the usage of all installed software is in keeping with the terms and conditions of the specific vendor license agreement. In doing so, organizations can minimize liabilities associated with software piracy in the event of an audit by a software vendor or a third party such as the Business Software Alliance (BSA). SAM, according to this interpretation, involves conducting detailed software inventories on a ongoing basis to determine the exact number of software licenses consumed, comparing this information with the number of licenses purchased, reviewing how the software is being used in respect to the terms and conditions and establishing controls to ensure that proper licensing practices are maintained on an ongoing basis. This can be accomplished through a combination of IT processes, purchasing policies and procedures, and technology solutions such as software inventory tools.
Counting installations is the most common means of measuring license consumption but some software is licensed by number of users, capital, processors or CPU Cores.
More broadly defined, the strategic goals of SAM often include (but are not limited to) the following:
- Reduce software and support costs by negotiating volume contract agreements and eliminating or reallocating underutilized software licenses
- Enforce compliance with corporate security policies and desktop/server/mobile standards
- Improve worker productivity by deploying the right kinds of technology more quickly and reliably
- Limit overhead associated with managing and supporting software by streamlining and/or automating IT processes (such as inventory tracking, software deployment, issue tracking, and patch management)
- Establish ongoing policies and procedures surrounding the acquisition, documentation, deployment, usage and retirement of software in an effort to recognize long-term benefits of SAM
SAM Technology
A number of technologies are available to support key SAM processes:
- Software inventory tools intelligently “discover” software installed across the computer network, and collect software file information such as title, product ID, size, date, path, and version.
- License manager solutions provide an intelligent repository for license entitlements which can then be reconciled against data provided by Software inventory tools to provide the organization with an ‘Effective License Position’ or view of where the organization is under-licensed (at risk of a compliance audit) or over-licensed (wasting money on unnecessary software purchases).
- Software metering tools monitor the utilization of software applications across a network. They can also provide real-time enforcement of compliance for applications licensed based on usage.
- Application control tools restrict what and by whom particular software can be run on a computer as a means of avoiding security and other risks.[6]
- Software deployment tools automate and regulate the deployment of new software.
- Patch management tools automate the deployment of software patches to ensure that computers are up-to-date and meet applicable security and efficiency standards.
- Request management tools allow employees to place requests for software products using a centralized form and process specifically designed to capture and assess specific license requirements as well as to manage and track the procurement and deployment process.
- Product catalog tools capture product specific information such as name, edition, version and license agreement types as well as other key top level information for products used within the business. This information normalizes product naming conventions with the organization and allows mapping between other technologies tools used in the composite SAM solution.